Risk-Based Vulnerability Management Solution
Verified risk-rated results.
Prioritized remediation.
Modern Strategy is Required to Manage Risk
While traditional vulnerability management (VM) systems help security teams identify, evaluate and fix vulnerabilities in their organization’s critical assets, evolving attack vectors in and out of the cloud pose a significant challenge to their effectiveness. The need for a greater understanding of cloud and endpoint resources, services, and their dynamics, is paramount to their protection.
Incorporating continuous threat intelligence with an accurate understanding of critical assets combined with prioritization based on key risk levels is essential to a responsive, modern VM strategy.
Risk Prioritization Cuts Through the Noise
Edgescan’s Risk-based Vulnerability Management (RBVM) solution reduces exposures by prioritizing remediation based on the level of risk posed to an organization by identifying, evaluating, and properly (re)configures the security of hybrid infrastructures to eliminate security blind spots. The
Edgescan RBVM solution is both pre-production and production safe providing ‘full stack’ coverage that includes web application, network layer (host/server) and API security testing.
Actionable, risk-rated vulnerability intelligence helps security teams ‘know where to focus first’ and understand exposure details, risk levels and accelerates response times.
Explore the Edgescan Risk-based Vulnerability Management Solution
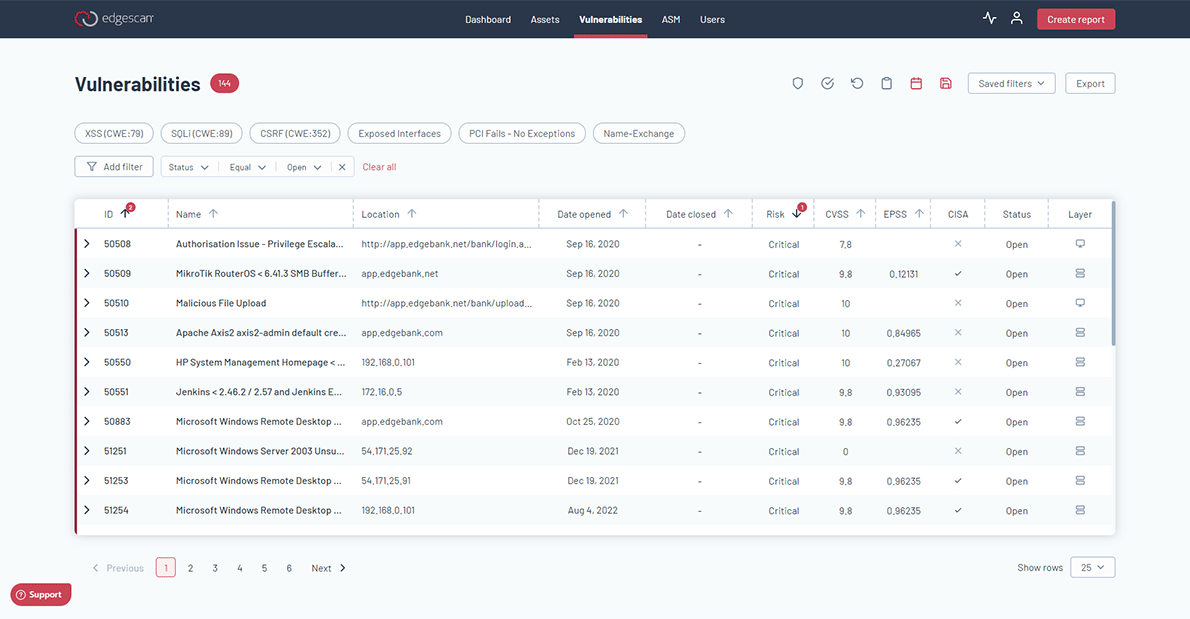
Risk-rated vulnerability data
Using automation combined with human intelligence, Edgescan uniquely tests for vulnerabilities that cannot be uncovered through traditional vulnerability scanning alone. Edgescan delivers validated vulnerability data and quickly rates the severity level of each exposure using a proprietary scoring process called EVSS (Edgescan Validated Security Score). Industry established risk-rating systems are also used:
- CVSS — Common Vulnerability Scoring System
- EPSS — Exploit Prediction Scoring System
- CISA KEV — CISA Known Exploited Vulnerability
Not all vulnerabilities are created equal – that is why Edgescan utilizes superior risk-based data to accelerate remediation.
Receive actionable risk intelligence with the ability to rescan on demand to ensure that your hosts and assets are fixed.
Expanding Data Lake of Vulnerability Intelligence
Our data accuracy is exemplified by our unique dataset being part of the Verizon Data Breach Report (DBIR), which is the de facto standard for insights into the common drivers for incidents and breaches today.
Key Benefits of Risk-based Vulnerability Management
Verified results ensure accuracy & eliminate false positives
Our hybrid approach ensures only real, prioritized, and actionable results are delivered eliminating the false positive ‘noise’ – reducing costs and saving time.
Risk-rated results with prioritized remediation
Employs risk-rating systems like CVSS EPSS, and CISA KEV, and our own EVSS score, resulting in superior risk-based data to enable accelerated identification of high-risk issues and rapid remediation.
Unlimited assessments. Unlimited retests.
Schedule an assessment at any time and retest on demand, as often as you like, ensuring accuracy of changes and providing peace of mind.
Progress tracking to understand vulnerability lifecycles
Utilizing risk-based metrics and KPIs effectively track and measure your security posture over time to show improvements of your security maturity and resilience.
Risk-Based Vulnerability Management Solution FAQ
What is software vulnerability management?
What is a vulnerability assessment solution?
What is a vulnerability scanner?
A vulnerability scanner is a software tool that scans computer systems, networks, or applications to identify security weaknesses and vulnerabilities. It automatically searches for potential entry points for cyberattacks, helping organizations assess their risk levels and take proactive measures to strengthen their defenses and protect against potential cyber threats.
What is a vulnerability management program?
Vulnerability management programs have a systematic approach to identify, evaluate, and address security vulnerabilities in an organization’s software, systems, and networks. It involves regular assessments, prioritizing risks, and implementing measures to mitigate threats, ensuring ongoing protection against cyberattacks and maintaining a robust cybersecurity posture.
Risk-based vulnerability management: What is it?
RBVM is the process of prioritizing and remediating vulnerabilities by the risk level that they pose to the organization.
Managing a cybersecurity risk assessment, how can organizations ensure proactive threat identification and mitigation?
To proactively identify and mitigate cybersecurity risks, organizations should conduct regular risk assessments, leverage threat intelligence, stay informed about emerging threats, and implement robust security controls. Continuous vigilance is critical.
Risk based vulnerability management vs traditional vulnerability management: Which one is better for managing vulnerabilities?
RBVM (Risk-Based Vulnerability Management) outshines traditional methods by prioritizing vulnerabilities based on risk impact. It’s a smarter, more effective approach for robust cybersecurity.
Vulnerability risk management tools: What do you need to look out for?
First, there are quite a few vulnerability management (VM) tools out there that cannot accomplish what they claim they are capable of, so thorough due process when selecting a VM tool is always recommended. Beyond VM tool capability, there are often resource constraints within the organization, and in most cases, expertise and experience around managing, configuring, and deploying VM tools. Last, even when all of this is accounted for and done properly, there are additional cycles required by an organization to ensure that the outputs of these tools are actionable (i.e., no wasting development cycles on false positives, having enough context and guidance around the remediation, support, etc.).
RBVM Solution: How can cyber security teams leverage it?
Edgescan RBVM is designed to augment an organization’s security team by eliminating the need to own, manage, and configure multiple tools such as network vulnerability scanners and DAST tools. Further, Edgescan RBVM presents only validated vulnerabilities to the platform so teams do not waste cycles on false positives.
Vulnerabilities in cybersecurity can pose significant risks. How can organizations systematically assess, prioritize, and mitigate these vulnerabilities to bolster their digital defenses?
Edgescan RBVM incorporates industry standard risk rating systems like NIST CVSS, along with third-party threat feeds like the CISA Known Exploited Vulnerabilities (KEV) Catalog, FIRST.org Exploit Prediction Scoring System (EPSS), along with propriety risk rating systems (i.e. Edgescan Validated Security Score (EVSS) and Edgescan Exposure Factor (EXF)), so organizations have the visibility and flexibility to determine the approach that is right for them.
How do you prioritize critical vulnerabilities based on risk and impact?
There are many different approaches to risk-based prioritization of vulnerabilities. Still, in general, the risk is determined by many factors, including but not limited to the sensitivity of the data that is potentially assessable if a breach were to occur, how likely a vulnerability is to be exploited, and whether the vulnerability is known to have been exploited.
How can risk-based management strategies help organizations identify and mitigate security risk vulnerabilities effectively?
RBVM (Risk-Based Vulnerability Management) empowers organizations to strategically prioritize and address cybersecurity risks. It’s about smartly managing vulnerabilities to enhance overall security resilience.
Risk-Based Vulnerability Management Solution FAQ
What is software vulnerability management?
Software vulnerability management refers to the process of identifying, assessing, prioritizing, and mitigating security vulnerabilities in software applications and systems. It aims to proactively detect weaknesses that attackers could exploit, leading to potential security breaches. By regularly patching, updating, and implementing security measures, organizations can reduce the risk of cyberattacks and enhance their overall cybersecurity posture.
What is a vulnerability assessment solution?
A vulnerability assessment solution is a software tool or service that scans and evaluates computer systems, networks, or applications to identify potential security weaknesses and critical vulnerabilities. It helps organizations detect and prioritize risks, allowing them to take proactive measures to strengthen their defenses and protect against cyber threats.
What is a vulnerability scanner?
A vulnerability scanner is a software tool that scans computer systems, networks, or applications to identify security weaknesses and vulnerabilities. It automatically searches for potential entry points for cyberattacks, helping organizations assess their risk levels and take proactive measures to strengthen their defenses and protect against potential cyber threats.
What is a vulnerability management program?
Vulnerability management programs have a systematic approach to identify, evaluate, and address security vulnerabilities in an organization’s software, systems, and networks. It involves regular assessments, prioritizing risks, and implementing measures to mitigate threats, ensuring ongoing protection against cyberattacks and maintaining a robust cybersecurity posture.
Risk-based vulnerability management: What is it?
RBVM is the process of prioritizing and remediating vulnerabilities by the risk level that they pose to the organization.
Managing a cybersecurity risk assessment, how can organizations ensure proactive threat identification and mitigation?
To proactively identify and mitigate cybersecurity risks, organizations should conduct regular risk assessments, leverage threat intelligence, stay informed about emerging threats, and implement robust security controls. Continuous vigilance is critical.
Risk based vulnerability management vs traditional vulnerability management: Which one is better for managing vulnerabilities?
RBVM (Risk-Based Vulnerability Management) outshines traditional methods by prioritizing vulnerabilities based on risk impact. It’s a smarter, more effective approach for robust cybersecurity.
Vulnerability risk management tools: What do you need to look out for?
First, there are quite a few vulnerability management (VM) tools out there that cannot accomplish what they claim they are capable of, so thorough due process when selecting a VM tool is always recommended. Beyond VM tool capability, there are often resource constraints within the organization, and in most cases, expertise and experience around managing, configuring, and deploying VM tools. Last, even when all of this is accounted for and done properly, there are additional cycles required by an organization to ensure that the outputs of these tools are actionable (i.e., no wasting development cycles on false positives, having enough context and guidance around the remediation, support, etc.).
RBVM Solution: How can cyber security teams leverage it?
Edgescan RBVM is designed to augment an organization’s security team by eliminating the need to own, manage, and configure multiple tools such as network vulnerability scanners and DAST tools. Further, Edgescan RBVM presents only validated vulnerabilities to the platform so teams do not waste cycles on false positives.
Vulnerabilities in cybersecurity can pose significant risks. How can organizations systematically assess, prioritize, and mitigate these vulnerabilities to bolster their digital defenses?
Edgescan RBVM incorporates industry standard risk rating systems like NIST CVSS, along with third-party threat feeds like the CISA Known Exploited Vulnerabilities (KEV) Catalog, FIRST.org Exploit Prediction Scoring System (EPSS), along with propriety risk rating systems (i.e. Edgescan Validated Security Score (EVSS) and Edgescan Exposure Factor (EXF)), so organizations have the visibility and flexibility to determine the approach that is right for them.
How do you prioritize critical vulnerabilities based on risk and impact?
There are many different approaches to risk-based prioritization of vulnerabilities. Still, in general, the risk is determined by many factors, including but not limited to the sensitivity of the data that is potentially assessable if a breach were to occur, how likely a vulnerability is to be exploited, and whether the vulnerability is known to have been exploited.
How can risk-based management strategies help organizations identify and mitigate security risk vulnerabilities effectively?
RBVM (Risk-Based Vulnerability Management) empowers organizations to strategically prioritize and address cybersecurity risks. It’s about smartly managing vulnerabilities to enhance overall security resilience.